About NTP
The Network Time Protocol (NTP) is a networking protocol for clock synchronization) between computer systems. Most commonly it runs on:
UDP port 123
Commonly used servers include: time.nist.gov, ca.pool.ntp.org, us.pool.ntp.org, etc
Most devices today wake up (boot up) and the first question they ask is “What time is it?” They do this by having built-in default servers to connect to, which dutifully listen on UDP port 123.
Why it is a security concern
NTP servers can be misused and abused and naturally, network and system administrators do not want any of their hosts to participate in such a UDP or NTP reflection attack.
Furthermore, since it is traditionally a clear-text protocol, time synchronization can be interfered with and used in attacks on endpoints which depend on it.
Since ADAMnetworks mission is to protect people, the NTP component needs to be addressed.
How to reduce the attack surface and serve NTP internally
There are simple and straight forward steps that anyone can take that has a router capable of running NTP server. In this article we’ll outline how we achieve it on pfSense®. Broadly speaking, it is these easy steps:
- Enable NTP server service.
- Create a Firewall Allow rule on each network segment.
- Adjust DHCP service to offer internal NTP services.
- Create a NAT rule to hijack all non-local internet-bound NTP queries.
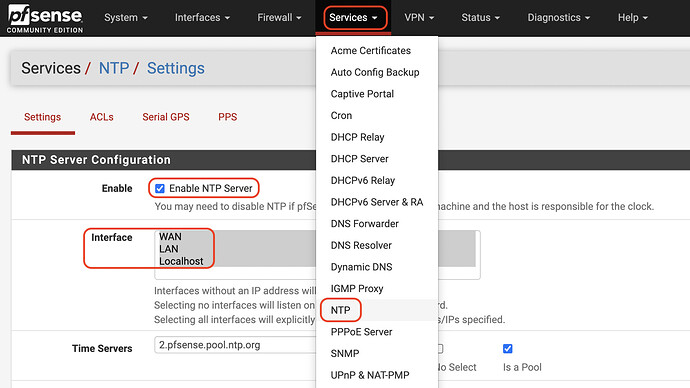
Enable NTP Server
From the GUI, select Services → NTP and Enable it on all interfaces, including WAN and localhost as shown here:
In most cases, the remaining settings can remain at their defaults. The reason we include WAN in the interface bindings is for compatibility. The WAN firewall won’t be responding so it isn’t a public-facing service as it appears to be.
Remember to Save Settings.
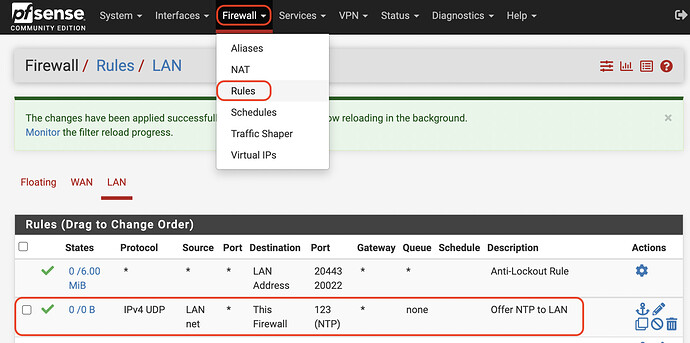
Create a Firewall Rule on each network segment
In a Zero Trust Connectivity mode, all access to the gateway that is expected to function needs to be specified, so a rule like this is essential:
Repeat this on each internal LAN segment. Alternatively, a single Floating Rule may be more appropriate in environments with many network segments.
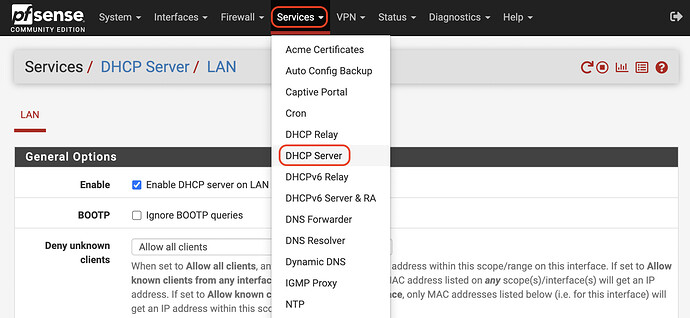
DHCP Server Changes
From Services → DHCP Server like this:
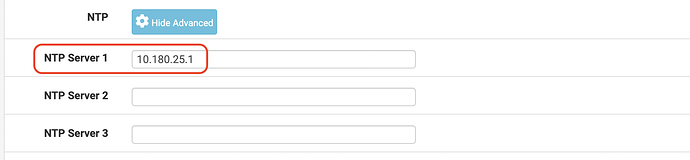
Enable NTP Services like this:
Specifying your gateway (or CARP address, in the case of HA) as the NTP Server 1.
Remember to Save settings.
Create a NAT hijack rule
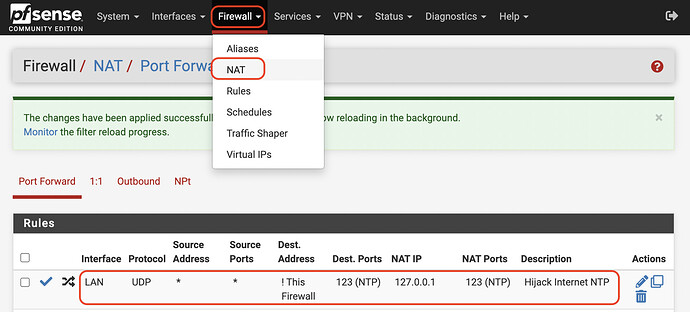
From Firewall → NAT menu, we create a Port Forward rule on each LAN segment:
What you’re telling your gateway is that any traffic attempting to reach UDP port 123 at a destination that is not This Firewall, should be Network Address Translated to itself (127.0.0.1).
This is what provides each endpoint with both security (avoiding NTP/UDP reflection attack participation) while at the same time offering it the answer it is legitimately after: The time is now 9:41. In other words, the endpoint may have asked someone on the Internet, but the gateway gave it the answer instead.
Note that for endpoints using NTPv3 (which includes authentication), this hijacking rule will prevent the endpoint from setting its time. If a device is no longer keeping time, it is recommended to adjust the endpoint to use DHCP-provided NTP services, or statically assign NTP field values with your internal LAN IP/hostname.
Managed Services
As of 2022, this is the standard deployment for all new/renewed managed clients.